DISCLAIMER: Links included might be affiliate links. If you purchase a product or service with the links that I provide I may receive a small commission. There is no additional charge to you.

The Resistance Hub
March 17–24, 2025
Fires, Fiber Cuts, Laws, and Leaks: Global Resistance and Sabotage in Focus
In today’s turbulent global security environment, irregular warfare has become the method of choice for many state and non-state actors. It allows them to shape political, military, and economic outcomes without entering open, declared conflict.
Over the past week, this approach was on full display. Incidents combined sabotage, cyber attacks, and legislative measures to disrupt systems and influence public perception.
From railway sabotage in Crimea to suspected eco-terrorist attacks in Norway, the period between March 17 and 24 saw a sharp rise in disruptive operations. These targeted infrastructure, information networks, and governance structures. Each episode reflects deeper trends shaping contested spaces in Europe, East Asia, and the expanding digital battlefield.
This report covers the most significant irregular warfare events—kinetic and cyber, overt and covert—and shows how they connect to broader strategic goals.
France — Coordinated Sabotage of Telecom Infrastructure Near Paris

On March 22, coordinated sabotage attacks targeted fiber optic infrastructure in the Île-de-France region. Underground cable conduits near Nozay were deliberately severed. The damage affected major telecom providers, including Free and Orange.
The result was widespread disruption. Internet services went down. Mobile networks failed. ATM systems also stopped working. Thousands of users across the Paris metropolitan area were impacted.
French authorities have not publicly identified suspects. The incident resembles similar attacks in 2022 and 2023 linked to ultra-left anarchist cells. These groups opposed the 5G rollout and claimed to resist what they see as growing state surveillance. In today’s tense geopolitical climate, some officials have not ruled out the involvement of foreign state proxies. Such actors may be testing French civil resilience.
This “low-tech but high-impact” method—cutting key network cables—highlights the vulnerability of modern societies to small, targeted acts of sabotage.
Crimea — Atesh Partisans Strike Russian Rail Line
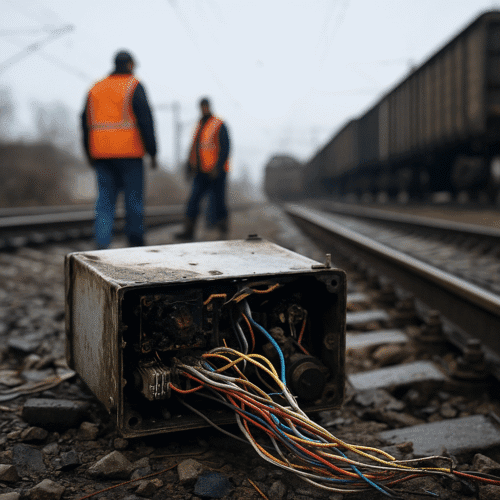
On March 20, Ukrainian resistance group Atesh claimed responsibility for sabotaging a railway near Stolbove in Russian-occupied Crimea. The group reported that a covert operative destroyed a signaling relay cabinet controlling supply lines toward the Zaporizhzhia front.
Satellite imagery released afterward appeared to confirm the disruption, showing emergency maintenance crews on-site and visible rail delays. This attack fits into Ukraine’s wider partisan warfare campaign behind enemy lines—low-visibility sabotage actions designed to create outsized disruption to logistics and force allocation.
While the Ukrainian government rarely confirms Atesh’s operations directly, the group’s activities align with broader military objectives and demonstrate how resistance movements can strategically integrate sabotage into national defense.
Hong Kong — Sweeping Anti-Subversion Law Enacted

On March 19, Hong Kong’s Legislative Council unanimously passed the Safeguarding National Security Law. This long-anticipated legislation criminalizes treason, sedition, and “external interference.” It introduces life imprisonment penalties and gives authorities the power to conduct closed-door trials.
Analysts view the law as a watershed moment for Hong Kong. Many believe it will drive organized dissent underground. Civil society leaders warn of a possible “Second Resistance Wave.” Activists may turn to encrypted communication, self-exile, and covert protest networks to sustain opposition.
From an irregular warfare perspective, Hong Kong could become a new arena for soft-power resistance. Exiled activists may serve as external information warfare hubs, while covert networks operate inside the city. Beijing describes the law as a safeguard against Western influence. However, its sweeping scope could harden ideological resistance, especially among younger generations.
United Kingdom — Heathrow Airport Disrupted by Suspicious Fire

On March 21, a suspicious electrical fire broke out at a major substation serving Heathrow Airport. The incident forced the grounding of flights, caused cascading delays, and disrupted air traffic across Western Europe.
Officially attributed to a systems failure, the fire’s timing and location have raised questions among security analysts. Substations of this type are critical to operations yet rarely fail without prior warning, making them potential soft targets for disruption.
Given Heathrow’s role as one of the world’s busiest air travel hubs—handling over 1,300 flights daily—an incident here can cause strategic-level disruption without the need for large-scale violence. While no group has claimed responsibility, the event follows a pattern of infrastructure-targeted incidents in the UK over the past year. Investigators are reportedly considering far-right extremists, Russian-aligned actors, and anarchist networks as potential culprits.
Norway — Large-Scale Oil Leak Suspected as Sabotage
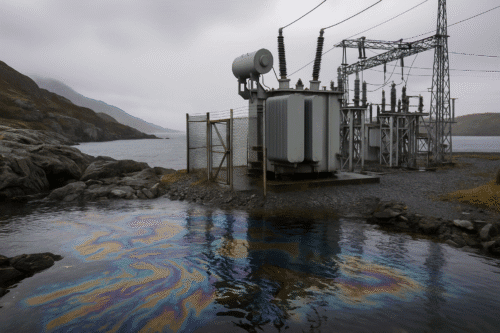
On March 17, authorities in Oslo responded to an environmental emergency after more than 60,000 liters of insulating oil leaked from a disused transformer station owned by Statnett, the national grid operator. Police confirmed signs of forced entry, and the company has stated the leak may have been caused by deliberate tampering.
Norway plays a pivotal role in Europe’s energy security, particularly since the sabotage of the Nord Stream pipelines. This incident, therefore, carries both environmental and geopolitical weight.
Investigators are exploring multiple possibilities, including eco-terrorism, extremist activism, or foreign state-linked operations—with some pointing to potential Russian involvement given tensions in the High North and North Sea.
Cyber and Information Warfare — AI Weaponization on the Rise

On March 18, Europol released a report warning of a rapid increase in the use of artificial intelligence by criminal syndicates operating as proxies for state actors. These groups have been utilizing AI to expedite phishing attacks, automate malware generation, and create highly convincing deepfake propaganda.
Russia and China are cited as the primary backers, often channeling such activity through semi-deniable contractors or dark web intermediaries. Europol emphasized that AI’s integration into cyber operations is transforming the tempo and psychology of irregular warfare—shortening decision cycles, complicating attribution, and amplifying narrative control.
United States — Hybrid Threat Countermeasures Scaled Back

On March 19, the Trump administration announced the suspension of several national security programs aimed at countering Russian disinformation, sabotage, and cyber intrusion. Specifically, the affected initiatives include work by the State Department’s Global Engagement Center and the Pentagon’s hybrid warfare task force.
According to the administration, this move is part of an effort to reset diplomatic relations with Moscow. However, critics argue it leaves the United States exposed to evolving gray-zone activity. In addition, analysts warn that scaling back these defenses may create exploitable gaps. This risk is particularly concerning at a time when Russian hybrid operations are adapting to bypass conventional countermeasures.
North Korea — Establishment of ‘Center 227’ for AI-Driven Cyberwarfare

Intelligence from South Korea and the United States confirms that North Korea has created Research Center 227, a cyberwarfare unit under the Reconnaissance General Bureau. The center’s mission includes developing AI-enabled malware, penetrating financial systems, and conducting destabilizing propaganda campaigns.
North Korea has previously demonstrated disproportionate cyber capabilities, most notably through the WannaCry ransomware attack and large-scale financial thefts. The creation of Center 227 signals a strategic shift from financially motivated cybercrime to broader asymmetric warfare, with AI as a central enabler.
Key Takeaways — A War Without Frontlines
- Infrastructure remains a prime target, with fiber optic networks, energy grids, rail lines, and airports all disrupted in the same week.
- Artificial intelligence is reshaping cyber operations, making them faster, harder to attribute, and more psychologically impactful.
- Legislation can function as a weapon, as seen with Hong Kong’s sweeping new security law.
- Attribution is critical—without it, shadow actors operate with impunity.
Final Analysis — Resistance Is Adapting
From Hong Kong’s crackdown to Norwegian oil sabotage, these events illustrate that irregular warfare is no longer just the tool of the weak. It is now a shared strategic domain in which resistance movements, major powers, and criminal proxies all operate—often in overlapping theaters.
This week’s incidents reinforce a reality that policymakers and military planners must confront: modern conflict is waged in silence, shadows, and systems. In this environment, disruption, perception, and timing often outweigh territorial control.
For a consolidated list of organizations, research centers, and training institutions focused on irregular, hybrid, and asymmetric warfare, visit our [resources page].
Leave a Reply