In the battles of the 21st century, the frontlines are rarely marked by barbed wire or tank traps. Instead, the decisive blows often land silently, deep inside enemy territory, disrupting logistics, crippling morale, and fracturing trust — all without a single shot fired. This is the domain of sabotage, the quiet engine of hybrid warfare.
Where conventional warfare seeks to destroy armies, hybrid warfare seeks to destabilize societies. It blurs the lines between war and peace, between combatant and civilian, between reality and perception. Sabotage, once seen as a supplementary tactic of guerrillas and resistance fighters, has reemerged as a primary weapon, not just for irregular actors but for states themselves. In recent years, its use has accelerated in conflicts ranging from Ukraine to South Asia, offering a window into the evolving logic of modern warfare.
At its core, sabotage in hybrid conflict is not about spectacular destruction. It is about pressure — precise, cumulative, and psychologically corrosive. And it is rapidly becoming one of the most potent forms of irregular power projection in an unstable world.
Since this article’s publication in April 2025, hybrid sabotage has escalated to unprecedented levels across Europe. Intelligence assessments from GLOBSEC and the ICCT documented a fourfold increase in Russian sabotage operations across Europe in 2024 compared to the prior year, with the surge accelerating through 2025. By early 2026, the Munich Security Report counted more than 150 suspected hybrid incidents across EU and NATO member states. Germany alone recorded 321 suspected sabotage attempts in 2025.
Key developments include a November 2025 rail bombing in Poland on a viaduct that could have killed dozens, linked to GRU-recruited operatives; a Norwegian dam cyber-attack in which pro-Russian hackers seized control of a valve for four hours via weak ICS credentials; and an unprecedented surge in NATO airspace violations — 30 suspected drone incursions between September 2025 and January 2026, exceeding the total from the prior three years combined. NATO has launched Baltic Sentry to protect undersea infrastructure, and the EU imposed its first FIMI sanctions against Russian disinformation operatives in January 2026. Analysts at GLOBSEC warn that if peace negotiations collapse or U.S. support for Ukraine diminishes further, hybrid operations will likely intensify throughout 2026. Russian Sabotage in Europe →
Sources: GLOBSEC (2026), ICCT Hybrid Threat Tracker, Recorded Future Insikt Group, Munich Security Report 2026, France 24, NPR.
The Return of Sabotage: Old Tactic, New Context
Sabotage has always been a weapon of the weak against the strong. From the French Resistance derailing Nazi trains in World War II to insurgents targeting oil pipelines in Iraq, it has offered asymmetric leverage where conventional battles were unwinnable.
But in today’s hybrid warfare environment, sabotage has evolved beyond isolated acts of destruction. It is integrated into broader campaigns that weave together cyberattacks, information operations, economic coercion, and diplomatic pressure. It is strategic rather than tactical — designed not merely to damage, but to confuse, exhaust, and paralyze adversaries across multiple domains.
Recent incidents suggest that modern saboteurs are not looking for high body counts or dramatic headlines. They are seeking cumulative effects: persistent disruption of logistics, degradation of economic output, erosion of public confidence in security, and fracturing of societal cohesion.
In this sense, sabotage has become a quiet but central pillar of hybrid warfare, and its reach is expanding.
Sabotage Across the Globe: A Survey of Recent Operations
Over the past two years, the world has witnessed a wave of sabotage incidents, which, although individually muted, collectively underscore the central role sabotage plays in hybrid conflicts.
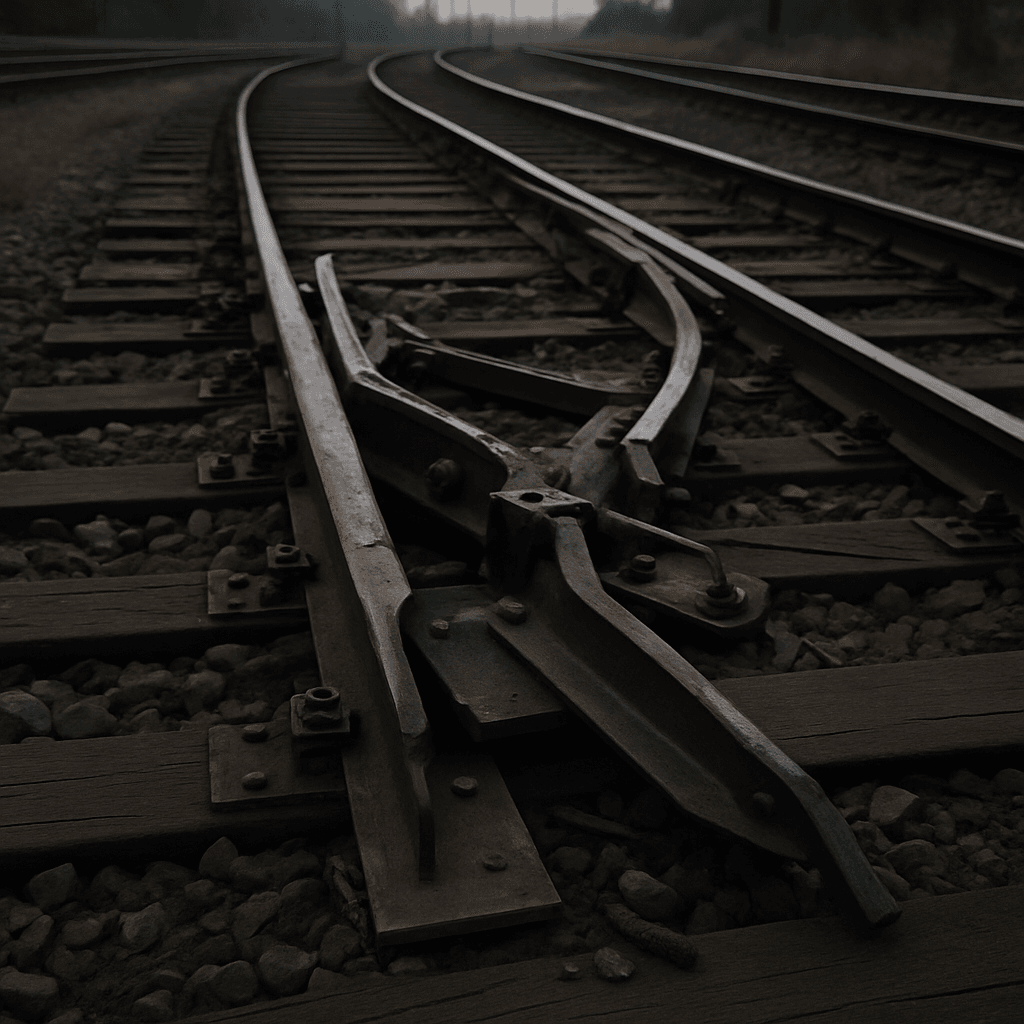
In India, a disrupted plot in Tamil Nadu aimed to derail trains along critical supply routes. Though swiftly intercepted, the plot highlighted the vulnerability of rail networks that underpin both civilian mobility and military logistics. Authorities have remained tight-lipped about the broader network behind the plan, but sources suggest external actors sought to sow chaos in a politically sensitive region.
Iran’s Industrial Explosions
Thousands of kilometers to the west, in Iran, a major explosion at an industrial facility near Bandar Abbas again raised the specter of covert sabotage. Official reports attributed the blast to technical failures — as they often do — but patterns seen over the past five years suggest a more complex picture. Industrial fires, explosions at nuclear sites, and power grid disruptions in Iran increasingly bear the fingerprints of deliberate operations rather than simple accidents. Each incident erodes the perception of regime competence and economic resilience. For a deeper look at the role of Iran’s irregular warfare apparatus, see The Resistance Hub’s analysis of Tehran’s proxy networks and covert capabilities.
Moldova’s Political Sabotage
Meanwhile, in the small republic of Moldova, sabotage has taken a political form. Intelligence services recently exposed what they described as a Russian-backed plot to replace Moldova’s government with more Kremlin-friendly figures. The operation reportedly combined cyber intrusions, disinformation campaigns, and clandestine funding of political actors — sabotage not of infrastructure, but of sovereignty itself. This pattern of political subversion mirrors techniques documented across Eastern Europe, where Moscow has repeatedly sought to fracture pro-Western coalitions through covert action.
Rail Disruption in South Africa
Even South Africa’s economic heartland has not been immune. A renewed focus on sabotage of coal transport railways in Richards Bay surfaced in March, with local union officials raising alarms about what they described as intentional acts of industrial disruption. As African economies grow more intertwined with global supply chains, the vulnerabilities exposed by sabotage become international problems.
And perhaps most alarmingly for the West, the Dutch Military Intelligence and Security Service (MIVD) revealed a sustained Russian campaign of cyber sabotage targeting NATO critical infrastructure. Far from crude attacks, these operations focused on ports, communication networks, and energy grids — systems whose disruption could have cascading effects on military readiness and economic stability across Europe. The Finnish rail sabotage incidents and suspected tampering with undersea internet cables in the Baltic Sea further illustrate the geographic breadth of this campaign.
In each case, the goal was not to win battles in the traditional sense; instead, it was to create a permanent state of vulnerability — economic, political, and psychological.
The Logic of Sabotage in Hybrid War
The strategic value of sabotage in hybrid conflict lies in its deniability, its disproportionate impact, and its capacity to corrode the will to resist.
First and foremost, sabotage offers plausible deniability. Bombs can be traced; missiles leave radar signatures. However, a derailed train, a mysterious warehouse fire, or a widespread cyber outage can often be attributed to human error, aging infrastructure, or random chance. Attribution becomes a political question, not a forensic certainty. This allows attackers to exert pressure without inviting open retaliation — a precious advantage in a world where escalation can have unpredictable consequences.
Second, sabotage is cost-effective. It is far cheaper to destroy a bridge than to rebuild it. It is far more affordable to knock out a rail switching station than to defend every inch of supply line. A single successful operation can cause millions in damages, delay military deployments, or disrupt elections at a fraction of the cost of a conventional military operation.
Finally, sabotage attacks the will to resist rather than merely the means. Repeated minor disruptions generate frustration, uncertainty, and despair. Citizens lose faith in their leaders’ ability to protect them. Militaries are forced to divert resources from offense to defense. Economies falter under the weight of accumulated instability. Over time, this psychological erosion can accomplish what confrontation cannot.
Sabotage, in short, is hybrid warfare’s scalpel — and it cuts deeper than many realize.
The Marriage of Cyber and Physical Sabotage
One of the defining features of modern sabotage is its fusion with cyber capabilities. Today’s hybrid saboteurs are not just placing explosives or derailing trains; they are hacking into control systems, corrupting sensor data, and weaponizing the interconnectivity of modern societies.
The Dutch MIVD report highlighted how Russian actors have targeted operational technology networks that control port logistics, power distribution, and transportation systems. In some cases, malware was inserted months in advance, lying dormant until activated in coordination with physical operations. This pattern of pre-positioning aligns with the broader doctrine of espionage-enabled sabotage, where intelligence collection and operational access merge into a single workflow.
This cyber-physical coupling offers two significant advantages. First, it enhances deniability. A bridge collapse caused by manipulated sensor readings appears to be an engineering failure, not an act of sabotage. Second, it increases effectiveness. Cyberattacks can neutralize security systems, delay responses, and maximize the damage of kinetic attacks.
The battlefield is no longer limited to physical space. It extends into code, into data streams, into the invisible architecture that sustains modern life. Sabotage has evolved accordingly, and defenders are struggling to keep pace.
Choosing the Target: Precision in Pressure
Modern saboteurs do not choose targets randomly. They seek points of maximum leverage — where limited action produces disproportionate systemic stress.
Strategic choke points, such as ports, railway junctions, and pipeline nodes, are prime targets for attack. Sabotage here can ripple through entire regions, stranding goods, delaying troops, or cutting off energy supplies. The protection of critical infrastructure has become one of the defining security challenges of the decade.
Symbolic targets — iconic buildings, government facilities, and cultural landmarks — offer psychological dividends, undermining public morale and broadcasting a sense of powerlessness.
Network fragility is another vulnerability. Power grids, telecommunications networks, and financial systems operate on tight tolerances. Minor disruptions at key nodes can cascade into widespread outages, creating economic and social turmoil far beyond the immediate point of attack. The German naval sabotage incidents of 2024–2025, in which warship systems were tampered with by foreign operatives, demonstrated that even military assets in home ports are not immune.
Modern sabotage campaigns are not about dramatic single strikes. They are about cumulative pressure — turning systems brittle, turning societies anxious, and forcing adversaries into costly, defensive postures.
The Challenges of Defense
Defending against sabotage in a hybrid warfare environment is a uniquely challenging task.

Attribution remains a significant obstacle. Governments are often reluctant to admit when sabotage succeeds, fearing it may appear weak or incite panic. Investigations usually take weeks or months, by which time the psychological damage — the fundamental objective — has already been done.
Resource asymmetry is another problem. It is prohibitively expensive to defend every piece of infrastructure, every port, every mile of railway. Attackers can afford to be selective; defenders must try to be universal.
Moreover, many institutions remain siloed in their approach to security. Cyber defenses are often separated from physical defenses; corporate security teams rarely coordinate with national intelligence agencies. Hybrid saboteurs exploit these seams.
Building true resilience against sabotage requires integrated defenses, rapid attribution capabilities, public trust management strategies, and an acceptance that no system can be entirely invulnerable. It demands a cultural shift as much as a technical one — a recognition that the information domain, the cyber domain, and the physical domain are no longer separable in modern conflict.
The Future of Sabotage: Smart, Decentralized, Psychological
As hybrid warfare matures, sabotage tactics are evolving in three primary directions.
First, automation. Drones, autonomous cyber tools, and remote-trigger devices allow small teams — or even individuals — to execute sophisticated sabotage operations with minimal risk of capture.
Second, decentralization. Inspired by insurgent and partisan models, modern sabotage networks operate with minimal centralized control. Small cells can operate independently within broad strategic frameworks, making detection and disruption significantly more challenging. Recent reporting has revealed that Russian intelligence services now recruit criminal proxies — including operatives from Colombia, Moldova, Serbia, and Bulgaria — through Telegram channels for sums as small as a few hundred euros, outsourcing deniable sabotage across the continent.
Third, psychological targeting. The goal of sabotage is increasingly not just to disrupt systems but to undermine the human decision-making processes that rely on them. Disinformation campaigns amplify the effects of physical attacks, creating confusion, panic, and apathy.
Sabotage will be less about destroying bridges and more about destroying the will to defend them. It will be about turning strength into perceived weakness, certainty into doubt, and stability into fragility.
In this new battlespace, visibility is a vulnerability. Trust is a target. And perception may matter more than reality.
Fourfold Increase in Russian Sabotage
ICCT and GLOBSEC document a fourfold surge in sabotage, arson, and vandalism operations across Europe compared to the prior year. Targets include logistics hubs, rail infrastructure, and defense supply chains. The GRU recruits criminal proxies from Moldova, Serbia, Bulgaria, and increasingly Colombia.
Classic Sabotage Drops; Airspace Violations Surge
Classic techniques (arson, vandalism) drop roughly 50% — possibly due to improved European counter-operations or Moscow’s focus on peace negotiations. But drone incursions into NATO airspace surge: 30 suspected violations from September 2025 to January 2026, exceeding the 23 recorded over the prior three years. Airports in Copenhagen, Oslo, and Munich are shut down. A Polish rail bombing in November nearly kills dozens. Pro-Russian hackers seize control of a Norwegian dam valve for four hours.
Year of Living Dangerously
Munich Security Report counts 150+ suspected hybrid incidents across EU/NATO states. Germany records 321 suspected cases. EU imposes first FIMI sanctions against Russian disinformation operatives. NATO launches Baltic Sentry for undersea cable protection. GLOBSEC and CEPA warn that if negotiations fail, hybrid operations will escalate further — particularly around European elections in Hungary, Sweden, and France.
Hybrid Incidents
German Cases (2025)
Airspace Violations
Sabotage Increase
Conclusion: Sabotage Is Strategy, Not Sideshow
The return of sabotage as a central pillar of warfare is not a historical curiosity. It is a fundamental feature of contemporary conflict. In the hybrid wars of the 21st century, the most decisive victories will often be won not on the battlefield, but in the shadows — through networks disrupted, economies shaken, governments destabilized, and publics demoralized.
Sabotage is no longer a supporting act. It is a strategy — silent, patient, cumulative, and devastating.
Those who fail to understand its evolving nature will find themselves defending against the wrong threats, too late, in a war they did not realize had already begun.
The battlefield is everywhere. The frontline is wherever a network switch hums, a train departs, or a population wonders who — or what — to trust.
In the age of hybrid war, sabotage is the silent weapon shaping the future.
Sources
The strategic framework for this analysis draws on Frank Hoffman’s foundational work on hybrid warfare in Joint Force Quarterly (2009) and Mark Galeotti’s research into Russian hybrid strategy at RUSI. The historical dimension of sabotage as a resistance tool is rooted in the OSS Simple Sabotage Field Manual (1944), available through the CIA’s declassified archive, and T.E. Lawrence’s Seven Pillars of Wisdom (1926). Gene Sharp’s From Dictatorship to Democracy (2002) and Gil Merom’s How Democracies Lose Small Wars (2003) provide the political science grounding for understanding sabotage within broader resistance and asymmetric conflict frameworks.
Reporting on recent incidents draws from BBC News coverage of European power outages, Radio Free Europe/Radio Liberty on sabotage operations in Ukraine, and Ukrainska Pravda on Russian sabotage groups. The escalation data for 2024–2026 is sourced from the GLOBSEC/ICCT Hybrid Threat Tracker, Recorded Future’s Insikt Group, and reporting by France 24 and NPR. Cyber-physical convergence analysis references the MITRE ATT&CK ICS framework and Thomas Rid’s Cyber War Will Not Take Place (2013).
Russian Hybrid Warfare by Oscar Jonsson — A detailed examination of how Moscow shapes conflict below the threshold of conventional war, tracing the doctrinal roots and modern applications of Russia’s hybrid approach.
OSS: Combined & Remastered — The Distillery Press edition brings together the foundational sabotage and intelligence manuals of the Office of Strategic Services, including the Simple Sabotage Field Manual referenced in this article.